When we all work, we save our pieces of information on the phone or the internet. While running a small business, we must have cyber security to protect it. You should also know about all the NIST cyber security Framework features and updates to work safely on the internet.
In the 21st century, it is essential to have cyber security to protect your data and personal information: health information, identification from any hacking and threats.
In this article, we will discuss the NIST cyber security Framework, how to manage it, and the benefits of having cyber security. We will also talk about where to translate the detected threat. You can also Check out Reasons For Outsourcing Your IT Solutions.
Table of Contents
What Is The NIST Cyber Security Framework?
NIST is the abbreviation for the National Institute of Standards and Technology. NIST framework helps to manage and reduce cyber security risks and threats for small or large businesses in the United States.
A framework is to give guidelines or ideal paths to follow afterward. NIST cyber security framework is a security control set that aligns with the Risk Management Framework (RMF). The framework aims to advance public and private organizational cyber security. It is intended for application at all levels of an organization, spanning from high-level strategic planning down to tactical implementation.
Visit: NIST Institute
See also: SOC 1 vs SOC 2 vs SOC 3 – All The Differences You Need to Know
Features Of NIST Cyber Security
The features of the NIST cyber security framework are divided into core, Tier, and Profile.
Core Features
The core features of the NIST cyber security Framework are mentioned here.
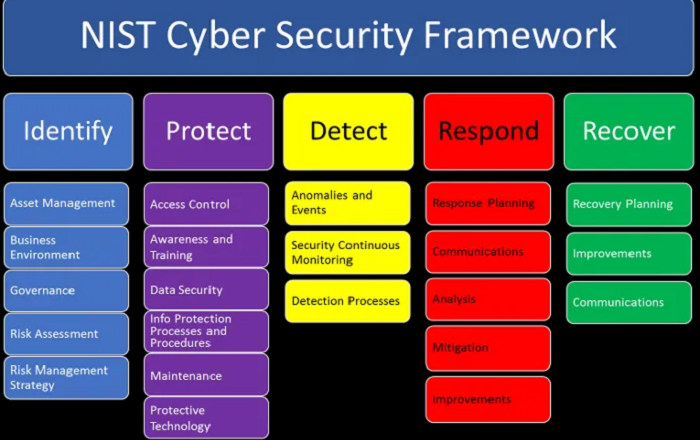
Identify, protect, detect, respond, and recover are the core features of the framework. The explanation for all, in brief, is given below.
Identify
The first thing is to identify the threats and understand them. Understanding the business and its contribution to the supply chain is important. The main focus here is to prioritize the efforts and update the business’s risk management strategy. This process consists of:
To identify all the physical and software assets to build the base of asset management, identify the business environment and contribution to the supply chain, and identify the policies and legal and regular requirements to have capable cyber security for the organization.
Protect
This feature gives the outline to protect and prevent cyber security harm to the business or the staff.
This product is meant to protect and manage all the identities as well as remote and physical access. It gives the training guidelines and awareness of the staff with cyber security. Also, it will provide information about how to manage and maintain the protection of this information. It is to plan a risk strategy to protect all the confidential and available data.
Detect
As the name suggests, Detect in NIST Framework is to define, monitor, and understand all the activities around the business. With SOC Prime’s Detection as a coding platform, you can hunt down all the inappropriate events or activities. SOC Prime Team also started an initiative of Uncoder.IO, a Sigma rule converter, to get all the information and knowledge about monitoring cyber threats.
Respond
Let’s say you were able to hunt down any cyber security event. This step is to ensure that there would be a response during and after that event. It is to manage communication with all the stakeholders. It determines the event’s impact and manages an effective response and recovery. You will be able to handle the reaction with SOC Prime Detector.
Recover
The scale of impact on the service depends on the cyber security incident. It is to ensure all the benefits and abilities are restored and renewed. It gives the guideline to ensure a recovery process to fix all the assets affected by the cyber security events.
To learn from the mistakes and improve the security of the organization. To effectively act with internal and external factors during and after recovery.
Tiers
Tiers in the NIST cyber security framework show an organization’s risk management stage. It is to represent the framework implementation stage. There are four tiers; Tier 1 (Partial), Tier 2 (Risk informed), Tier 3 (Repeatable), and Tier 4 (Adaptive).
Organizations must follow all their Tier rules and reach cyber security goals.
Profiles
The last step in the NIST cybersecurity framework is to set up a profile. This will be your Cyber Security Profile. You can customize it according to your business objectives, threat environment, and requirements & control.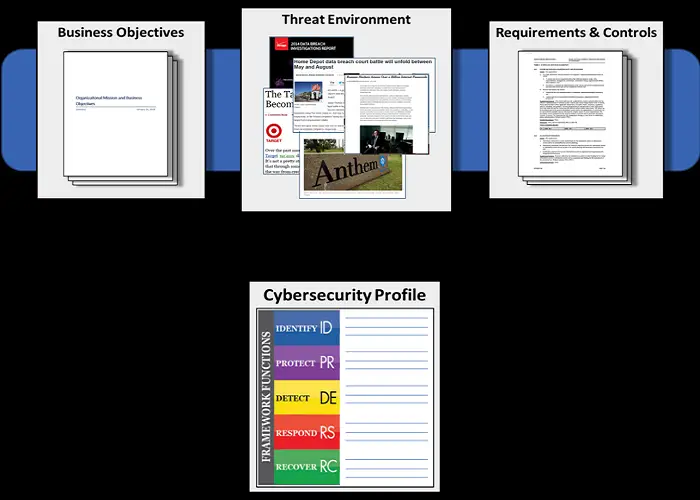
This Profile will help you to improve your cyber security and get the desired services from the Core Features.
Why Should You Use The NIST Cyber Security Framework?
You should use the NIST cyber security framework if you have faced any of the issues given below.
- Unseen risk and vulnerable activities.
- Proper protection of your assets.
- Your staff can be misled with useless information and may ignore the actual threat.
- Your team might not realize the impact of any cyber risks.
- You can utilize the tools to address the threats.
- Your board will question you regarding the risk management strategy without NIST.
See Also: Top 11 Cyberflix Alternatives
FAQs
What are the benefits of using the NIST cyber security framework?
By using the NIST cyber security framework you will get better knowledge about cyber risks, how to prioritize the activities, utilize the tool, and have better communication.
What are the steps of NIST CSF?
There are three steps of NIST CSF; Core feature, Tiers, and Cyber Security Profile.
What are the Core features of NIST CSF?
There are five core features of NIST. Identify, Protect, Detect, Respond, and Recover.
How many things can I manage with NIST CSF?
With the NIST cyber security framework, you can manage vulnerability, assets, risks, patch, vendor, and access control.
What is the use of the SOC Prime platform?
It can be useful to build advanced threat detection, plan a strategy and utilize all the security analytics tools.
Conclusion
With this full guide, you can manage your small business and protect it from all cyber security threats. NIST cyber security framework is a complete guideline to control, understand, prevent and protect all cyber security events.