Everything functions differently in the contemporary, extremely dynamic era of cyber security standards. If something travels in one direction, other objects may move in a different direction and accomplish the same goal. The article discusses some top Cybersecurity Standards.
Cybersecurity standards can help businesses identify defenses against online threats to their systems and data. They can also offer direction on handling and recovering from cybersecurity events. Regardless of their size or industry, all firms must meet security criteria. FISMA, HIPAA, FINRA, and other key cybersecurity regulations are just a few.
Although methods may vary, the objectives of cybersecurity work can still be achieved. In today’s dynamic cybersecurity landscape, organizations are gradually adopting more proactive strategies, such as conducting vulnerability assessments in cloud environments, to protect their digital infrastructure. Each region tends to implement its own cybersecurity regulations, leading to an increased reliance on top-tier managed detection and response (MDR) services in 2023.
Given the widespread nature of the Internet, it is crucial to uphold consistent Cybersecurity Standards globally. This consistency not only bolsters security effectiveness but also promotes integration and interoperability, allows for meaningful evaluations of different security methodologies, simplifies complex scenarios, and establishes a platform for ongoing innovation. Within this context, the subtle yet strategic application of thorough security assessments, similar to Bishop Fox’s cloud pen testing, becomes a critical element, reinforcing the collective commitment to uniform, effective cybersecurity measures.
Table of Contents
Cybersecurity Standards: What Are They?
A cyber security standard is a collection of guidelines that a company must follow in granting permission to do certain tasks, such as taking online payments, storing medical data, etc.
- The Cybersecurity Standards are some fundamental guidelines a business must follow to comply with all cybersecurity requirements.
- Depending on the business or organization’s needs, there are various standards from which to add particular capabilities.
- If you want to work for the government, you may have to abide by the government’s own rules in some regions.
- The set of regulations that must implement in the system to maintain any standard’s compliance is use to illustrate cybersecurity standards.

For instance, organizations must adhere to the PCI DSS standard if they wish to take payments online. The organization must abide by strict regulations that are part of this compliance to permit the process of online payments. Their system must be up-to-date, secure, and free of vulnerabilities. 
They also need to provide network reports frequently, and such requirements are part of the standards. The company is good to accept online payments if it can deliver useful reports; else, it will only allow requesting payment through its online interface.
See Also: NIST Cyber Security Framework | What Is It & How To Manage
Top 6 Standards for Cybersecurity
Following are the top cyber security standards:
ISO 27001
One of the common requirements a company must follow to create information on the Vulnerability Management system is this one. It consists of a collection of guidelines outlining the rules and conditions you must keep in mind before the organization can be certified by this standard.
According to these Cybersecurity Standards, the firm must maintain its technology at the most recent version, ensure its servers are secure, and undergo periodic audits to remain compliant. The ISMS policy, which covers ISO 27001 practice, must follow every organization that provides services to other organizations that comply with the international standard.
PCI DSS
The PCI DSS is abbreviated from Payment Card Industry Data Security Standard. An organization must use this standard when accepting payments through its payment gateway.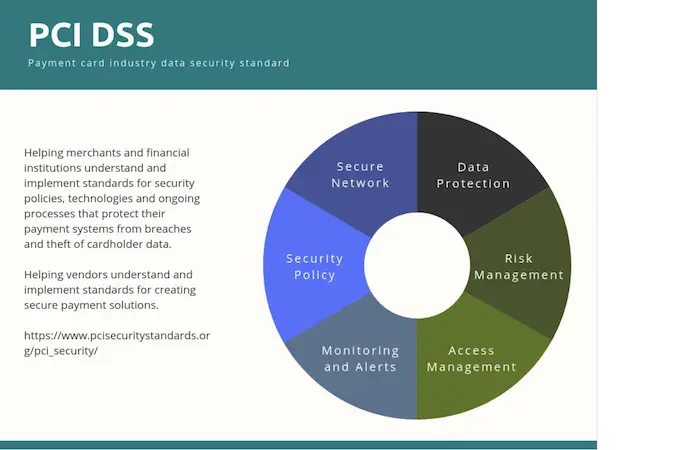
Businesses that keep customer information like names and card numbers must implement this standard. According to this compliance, the organization’s technology should be current, and its system should regularly go through a security review to ensure it doesn’t have any serious vulnerabilities. The card brands created this standard (American Express, Visa, MasterCard, JCB, and Discover).
FISMA
A US federal statute known as FISMA (Federal Information Security Management Act) was passed in 2002 as Title III of the E-Government Act. For all executive branch agencies, the law sets a comprehensive framework for guaranteeing the security of information and information systems.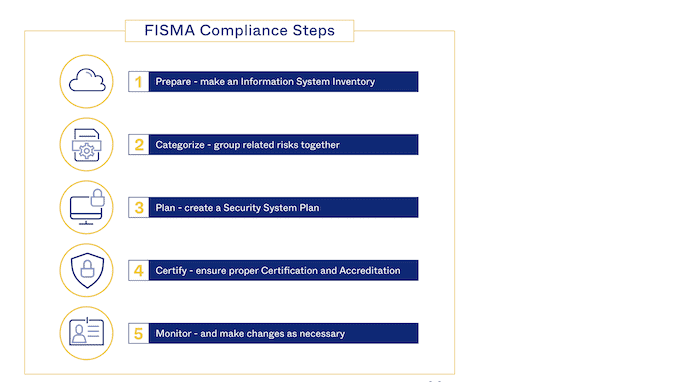
To improve information security inside federal agencies, NIST, and the OMB, the FISMA implemented (Office of Management and Budget). It mandates that federal agencies put information Cybersecurity Standards programs into place to safeguard the confidentiality, morality, and availability of their information and IT systems, including those supplied or managed by other agencies or contractors.
HIPAA
The Health Insurance Portability and Accountability Act is known as HIPAA. It is the standard that hospitals must adhere to guarantee that their patients’ data is completely protected and cannot leak in any way.
The hospital needs a capable network security team to handle all security incidents, strong quarterly security reports, encryption for all transactions, and other requirements to adhere to this standard. These Cybersecurity Standards guarantee that the patient’s sensitive health information will stay secure, allowing them to feel assured about their health.
FINRA
Financial Industry Regulatory Authority is referred to as FINRA. The main goal of these Cybersecurity Standards is to increase security for financial institutions that handle money or actively engage in financial operations.
This standard calls for a system to be extremely secure, and to comply with it, numerous steps in terms of data security and user data protection must be taken into account. It is one of the most important requirements that organizations with a financial foundation must meet.
GDPR
General Data Protection Regulation is referred to as GDPR. It is a standard established by the European Union, whose concern is for the privacy of all users. The organization responsible for overseeing compliance with this standard must ensure that user data is secure and cannot access without the appropriate authorization.
As implied by the name, the primary focus of this standard is on the security of the user’s data so that they may feel confident sharing it with any businesses that comply with the General Data Protection Regulation.
FAQs
What exactly are Cybersecurity Standards?
A security standard is a published stipulation that defines a common language, comprises a technical specification or other precise criteria, and is designed to use consistently, as a rule, a guideline, or a definition (National Institute of Standards and Technology).
What are the security requirements for the power sector?
It is a security standard for the electrical power sector that went into effect in 2003. NERC 1300 covers all of the power industry security requirements. CIP-002-3-CIP-009-3. 14.
What does cyber security aim to accomplish?
Cyber security standards aim to increase the security of vital infrastructures, networks, and information technology (IT) systems. A cyber security standard defines an information technology environment's functional and assurance requirements.
What are the standards for cyber security?
A list of requirements for managing cyber security risks includes in this standard. Additionally, it discusses a cybersecurity process paradigm that enables OEMs to share security risks on a unified platform.
Conclusion
The cybersecurity standards serve as a set of guidelines that specify the procedures or strategies that must maintain the system secure. Nearly every company performing at a higher level must adhere to the standards because those elements guarantee security. There are many cybersecurity standards on the market, and some new ones should be accessible by this year.
No matter the size, industry, or sector of the firm, cybersecurity frameworks are generally applicable. The basic cybersecurity compliance criteria that serve as a solid foundation for all cybersecurity strategies are here. Check this out to know more about IOC.


