Receiving an email that makes you doubt its authenticity is a sign of email spoofing and a request for information on how to stop it. While you contemplated whether to click the link, your heart started to beat a bit quicker. You are where hackers want you to be considering these options: uncertain. And when uncertain, we occasionally make fatal judgments in a single second.
You can stop email spoofing by using different passwords for different accounts; using a strong, challenging password; and changing your password often.
With the help of this blog, we’ll educate you about how to stop email spoofing and teach you how to spot and handle dangerous emails more effectively to keep you safe. Click here to find out the advantages and disadvantages of Email.
See Also: How To Reduce Bounce Rate Of Emails | Top 7 Tools
Table of Contents
What Is Meant By Email Spoofing?
Spoofing is a type of online fraud that involves fabricating an email message so that it looks as if delivered earlier than it was or to have originated from a different address. An ordinary instance of this would be a hacker sending an email with a link to a malicious website from what looks to be your firm’s domain name.
You can click on a link arriving from an address at your domain since you are familiar with it (for example, bemopro.com), but people advise you to stay cautious these days.
Email spoofing is altering email headers to make it look like a message was sent from a different address or location than it was. Moreover, fraudulent emails could include dangerous attachments that compromise your computer’s security by letting Trojans and spyware into your network. To put it simply, a dangerous email that seems completely innocent. One of the most popular techniques used by hackers to deceive unwary consumers into accessing websites intended for phishing and other types of cyberattacks is email spoofing.
One of the most popular techniques used by hackers to deceive unwary consumers into accessing websites intended for phishing and other types of cyberattacks is email spoofing.
Origin Of Email Spoofing
Hackers who wanted to get around IP address filtering, which allows you to control what IP traffic is permitted into and out of your network, invented email spoofing. Since then, it has developed into a method for hackers to use social engineering to persuade people to divulge critical information like passwords and other personal information. Let us look at the origin before knowing how to stop email spoofing. Several experts think the 1988 Morris Worm, notorious for sending spam emails, was where email spoofing first appeared. It wasn’t until 1999 that the earliest versions of email spoofing were widely known when cybercriminals began employing it to disseminate harmful links and phishing schemes.
Several experts think the 1988 Morris Worm, notorious for sending spam emails, was where email spoofing first appeared. It wasn’t until 1999 that the earliest versions of email spoofing were widely known when cybercriminals began employing it to disseminate harmful links and phishing schemes.
How To Recognize Email Spoofing (On Outlook)?
It can be challenging to identify email spoofs, especially when they come from sources with legitimate domain names (amazon.com, chase.com, etc.). Yet, there are methods you may use to tell if an email came from a different computer or was faked. Here are several methods for identifying fake emails:
Check to determine if the address in your “From” box corresponds to the sender’s actual address. This is, unfortunately, not a failsafe, as the attacker may utilize a hacked mailbox on the company’s email system rather than their email account. A dead giveaway is always an email that appears to be coming from an empty inbox. Check the email heading as well. In addition, look for any obvious typos or wrong nouns in the “To” column.
In addition, look for any obvious typos or wrong nouns in the “To” column.
Verify that you are also sending your responses to a valid email address. The easiest way to validate an email’s legitimacy is to contact the sender directly through a separate channel, such as by phone. Also, you may use free tools like MxToolbox to check whether a certain domain accepts PTR (pointer) records and SPF (Sender Policy Framework) data. You should assess whether the transmitting domain is reliable using these tools.
How To Recognize Email Spoofing(In General)?
Sadly, it’s difficult to tell if your email address has been faked. Probably, hackers have already exploited your email address for phishing schemes and other online assaults if it is exposed due to a data breach. Without requesting information about any current logins from Proxy servers besides your local region from your email provider, there is no guaranteed method to determine if someone has access to your email account. 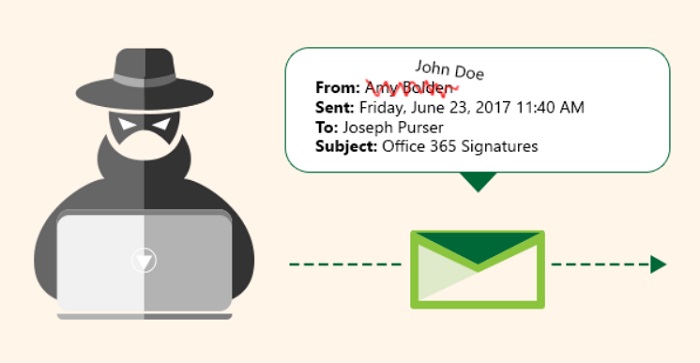 This makes it difficult to stop spoofing Emails.
This makes it difficult to stop spoofing Emails.
How To Stop Email Spoofing?
Therefore, you’re probably wondering how to prevent YOUR email address from being faked. There are, nevertheless, a few excellent practices, such as:
- Avoid using the same password across other accounts.
- Pick a strong, challenging password.

- Consistently change your passwords.
- Make your email account multi-factor authenticated.
To enable popular email security measures in Microsoft’s Exchange Online, follow the Comprehensive Email Security Guide in 5 parts. You need a special “Defender for Office 365” license to enable these security capabilities. Keep this in mind if you’re somewhat tech-savvy. Stay safe on the internet by following these practices.
What To Do On Receiving A Spoofed Email?
Indeed, fake emails may be harmful, and blocking spoofed emails seems viable. By using backdoor Trojans, they might direct you to websites intending to acquire your personal information.
Do not click any links in emails that appear suspicious or have odd links; report them immediately to your IT administrator. These links may lead you to websites intended for cybercrime if you click on them. Alert your IT administrator about the assault. They may update your company’s email policy and improve encryption for incoming and outgoing mail. This can prevent similar assaults from occurring in the future. The virus may hide frequently in any external discs connected to your computer. The virus scanner may identify the disc as having a dangerous program. It can provide you with instructions on how to remove it from your computer.
The virus may hide frequently in any external discs connected to your computer. The virus scanner may identify the disc as having a dangerous program. It can provide you with instructions on how to remove it from your computer.
See Also: 13 Best Free Fake Email Address Generator Tools
FAQs
Can you determine the source of a forged email?
Any information about the sender of an anonymous email, such as the sender's name, IP address, or metadata, cannot be used to identify the sender. This makes it difficult to enable a person from stopping email spoofing.
What is the most effective way of email spoofing prevention?
Utilize a Virtual Private Network (VPN) - By using a VPN, you can encrypt your traffic to keep it safe. Hence, even if your network is the target of an ARP spoofing attack, the attacker won't be able to read any of your data because of encryption.
What are the top 3 spoofing types?
Spoofing may take many forms, including fake emails, calls, GPS spoofing, websites, DNS spoofing, and emails.
How can I stop someone from using my email address?
It is impossible to stop someone else from accessing your email address. As spammers use a separate mail server, no solution can stop them from accessing your email address. It is not under the jurisdiction of Intermedia.
Conclusion
Cyber attackers commonly and harmfully use email spoofing to carry out their attacks. If you feel that you might be a victim, then you can consider a temporary mail redirection UK and use another secure email for the time being. For example, phishing and BEC (Business Email Compromise) assaults. Successful data breaches caused by email spoofing happen often.
About 22% of data breaches in 2019 involved email spoofing. Because of this, it is crucial to secure email protection and understand how to stop email spoofing. Also, know about finding someone’s email for free.
This manual will be your go-to resource for identifying appropriate solutions and protecting against email spoofing.


