In this evolving virtual, computerized domain and addiction toward electronic devices, another world uses its techniques to withstand any obstacle by non-standard or unauthorized means. It exploits the weakness in one’s system to gain access to its data. This is called the world of ‘hacking.’ You can also learn how to hack an android phone using cmd.
Electronic devices have become an intimate part of everyone’s life. This serves to be easier for the attackers due to various exposures. The central utilizing systems used are Android, IOS, Windows, Blueberry, etc.
But it is seen that people live in a society full of inconsistency and cannot safeguard their systems. So here’s a stepwise guideline for how to hack an android phone using cmd. Please go through these and get answers to any of your questions.
See also: How to Remove Cyber Police Virus in Simple Steps
What Does Hacking Any Phone Signify?
Phone hacking can concede one’s identity and intrude his secrecy without even knowing. Fortunately, you can protect your stuff by staying up to date and keeping yourself vigilant. Hacking any phone includes the complete knowledge of various situations in which attackers use security exploits to intervene in people’s confidential data.
This unauthorized access can be via different techniques like voicemail, handsets, or mobile phones. So also becomes necessary for you to know how to hack a phone using cmd.
See also: TechWhoop’s Guide To 13 Best Browsers For Android TV
Android Hacking Resources
For all those interested in android hacking apps, there are thousands of resources around the internet.
Below listed are a few of them:-
- Android exploits – it is an open source guide that hacks from GitHub users Sunday.
- XDA developer Forums- this is a hacking community with millions of users.
See also: Top 10 Best IP Camera Software for Security (Updated 2022)
Android Hacking Tools
Along with the manual tools, several applications are built to clear users’ queries on how to hack an android phone using cmd. 
Some of the popular ones are :
- Apktool
- Dex2jar
- JD-GUI
See also: PS4 Hacks You Probably Didn’t Know Existed!
Guidelines On How To Hack An Android Phone Using cmd
There are several ways that attackers might use to get control of your android devices.
It isn’t easy to hack any smartphones, so below are some ways to reason how to hack an Android phone using cmd :
Social Engineering
This is one of the most accessible and more widely used methods. Generally, smartphones have a stricter security system than PCs or servers because their application code prevents them from taking over the devices.
These applications do an essential job of segregating permissions to protect the users from rogue apps which can empty your data. This results in the appearance of a pop-up text to ask about one’s license. Hence this will prove to obstruct access to personalized data.
See also: How To Open Bin File On Android | Complete Guide
Malvertising
This includes all those deceptive texts which add along with the mobile advertising systems and brings about undesired changes invading one’s private information. These advertisements tempt the users to click on them while planning to scare them. This is their only goal.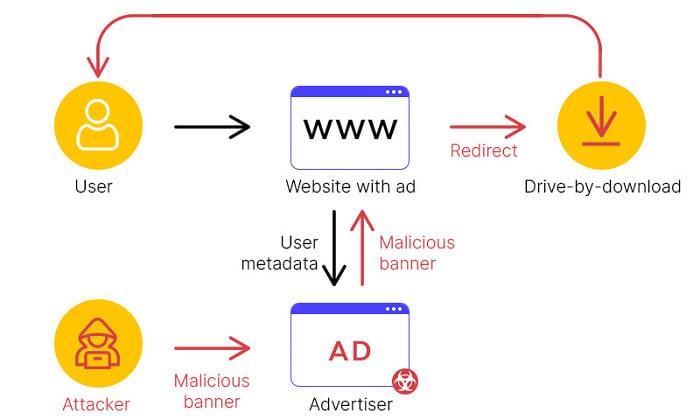
According to survey data, nearly 67% of these malicious apps originate in Google Play Store markets, while just a ratio of 10% belongs to alternative 3rd party markets. In the case of Apple, this is more secure because it closely inspects every app on its store, significantly reducing their chances of being malicious.
Smishing
This is just another vector that the attackers use to access their victim’s devices using SMS text messaging; they use different tricks to play with users; this practice is known as SMS phishing or smishing.
Cybercriminals utilize different ways of SMS messages depending on their intensity and intention to affect the users. Sometimes, hackers who use zero-day exploits can push a malicious file onto a phone without their consent.
See also: How to Remove Svchost.exe Malware From Windows
Malware
This involves jailbreaking of users’ phones by seeking out someone who’s already been done. This is done when the attackers cannot track the users by any other means. It involves relaxing the strict security sandboxing, preventing users’ phones from unlocking quickly.
This tricks innocent users into downloading malware onto their devices. Once downloaded, they start stealing personal information and other sensitive data. This also involves easy access to chats, passwords, etc.
Pretexting
This involves compiling together enough personal information about their victims in communications, thus gaining access to the victim’s account.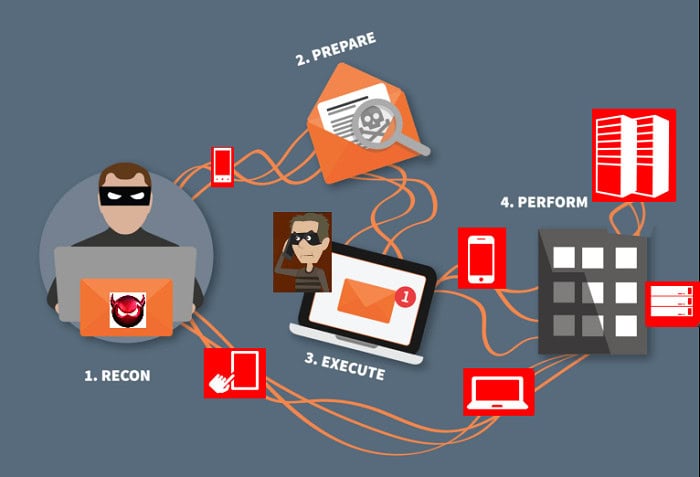
This provides complete access to victims’ phone calls, SMS, and other confidential data.
Breaking In Via Bluetooth
Hackers often use this method of connecting to devices by wireless means of Bluetooth as it is one of the weakest spots of an android phone. Hence providing users with the most straightforward answer to how to hack an android phone using cmd. 
Since most of the users keep their Bluetooth on, it becomes easier for the attackers to get access to the victim’s information, which is unrecognized.
See Also: Connect Bluetooth Headphones To Vizio TV
Man-in-the-middle Wifi Attacks
Many people connect their phones using free Wi-Fi, which paves the way for attackers to hack victims’ systems. This habit of users proves to be advantageous to clever hackers. It also comes under a potential wireless attack vector. This will help attackers to get personalized information regarding victims.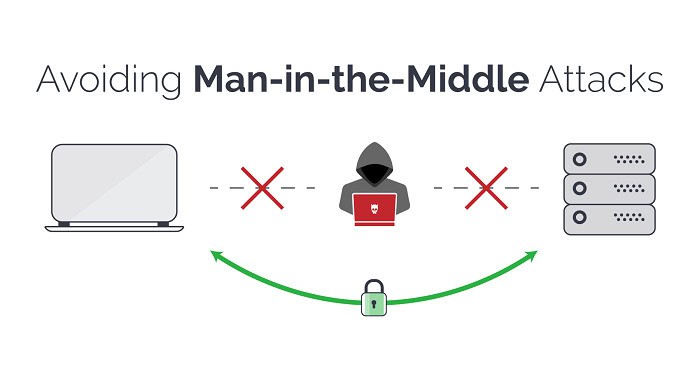
By the above-listed ways, one can learn valid information on hacking mobile phones with computers using cmd.
Brief Information About Sniffing And Sniffing Tools
A sniffer is a tool that can be either software or hardware. It allows users to take control of their internet trade. Also, it involves invading all the data exchange from your PC. It precludes the data packets traversing all across the network.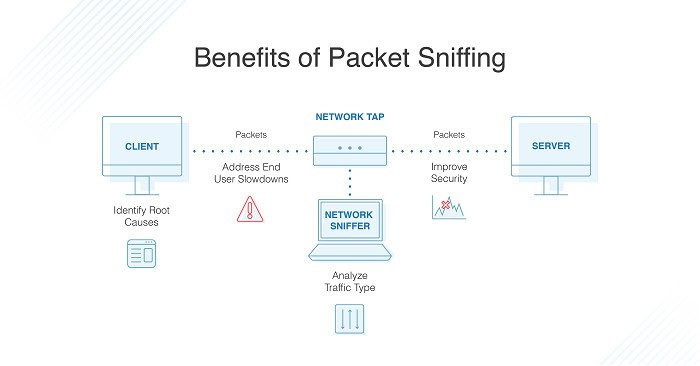
The Android sniffing tool is the thing for those who wish to access all activities on their android devices. Here are some of the best tools depicting how to hack into a phone using cmd :
- Wifi kill
- Wifi inspect
- Fing network tools
- NMAP for Android
- Insider
- Droidsqli Android App
- WPS connect etc
FAQs
How to know if your phone is hacked or not?
Attackers can risk users' phone security to get hold of confidential data. It depends upon the poor performance of your phone, Draining your battery, high data usage, unknown calls and texts, and unusual activities on the social handle. Here are several ways to know that.
What should be done once your android systems are hacked?
There are several ways of dealing with that, like resetting your phone services, running anti-malware apps, checking for suspicious and unnecessary apps, and unrooting your phone.
How to protect your systems from getting hacked?
To safeguard your Android, you can use some of these suggestions. It would help if you didn't store your passwords on your devices, Enable a lost device(GPS) tracking service, and always enable two-factor authentication in your device. It would help if you didn't jailbreak your phone. Also, it would help if you didn't use free public Wi-Fi without a virtual private network (VPN).
Conclusion
With the help of the above article, we hope to provide users with complete information on how to hack an android phone using cmd.
People around the globe are always in worry about their android’s security, and due to a lack of proper knowledge lend themselves to a lot of trouble.
There’s a vast difference between hackers and attackers, which is used in the above writing as hackers are just experimental people. In contrast, the latter comes under the category of criminals in computer systems to gain access to their data.
Through this, we tried to answer all your queries regarding the same.
See also: How to Remove Shortcut Virus from Pendrive / Computer
